State of Workforce Password Security Report 2026: AI Ambition vs Identity Reality
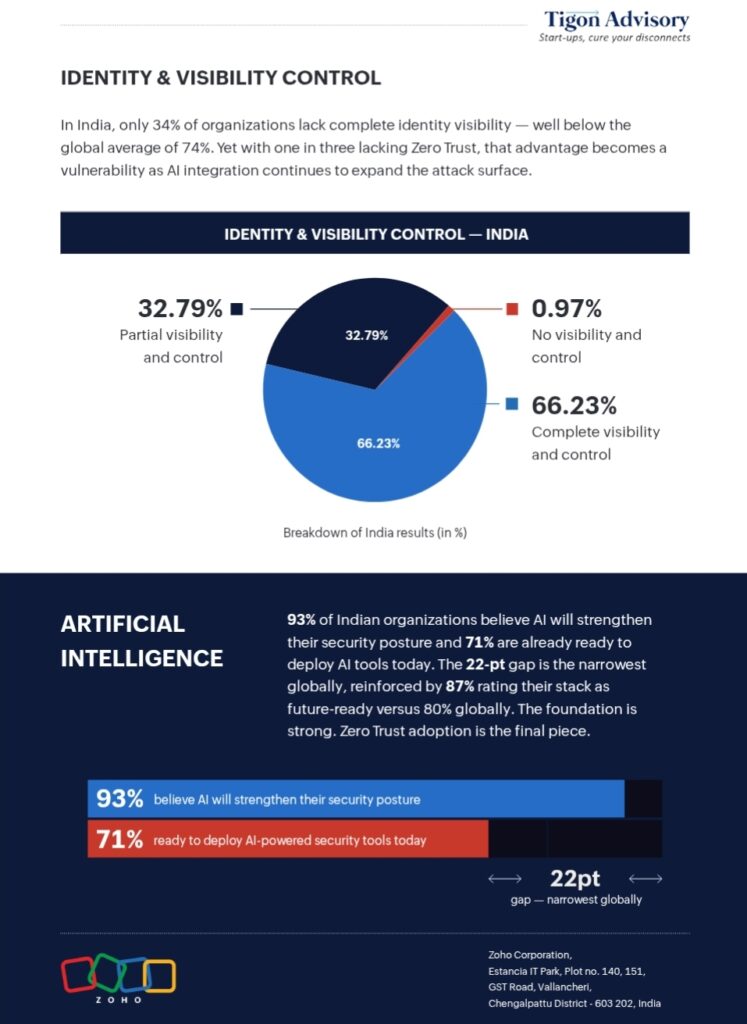
The State of Workforce Password Security Report 2026 surfaces a structural contradiction that goes beyond cybersecurity and enters the realm of customer experience design. Indian enterprises are accelerating toward AI-driven security, with 93% expressing confidence in its potential—yet one in three lacks a Zero Trust framework.
This is not just a technology gap. It is an architectural inconsistency.
The AI-Security Paradox Emerging in India
“While Indian businesses are keen to adopt AI, they still have blind spots, namely lack of Zero Trust, lack of visibility into their critical systems, and threats from internal sources.” — Chandramouli Dorai, Chief Evangelist, Cyber Solutions & Digital Signatures, Zoho Corp.
This becomes critical when AI expands access layers, multiplies credentials, and increases system interdependencies. The result is a widening gap between perceived readiness and actual resilience.
From a CX standpoint, this paradox manifests as both friction and fragility—users face inconsistent access experiences, while organizations remain exposed to internal and external threats.
Why State of Workforce Password Security Report 2026 Signals a Structural Shift
The deeper implication of the State of Workforce Password Security Report 2026 is not about password hygiene—it is about the transition from perimeter-based security to identity-centric architecture.
Historically, enterprises relied on:
- Network boundaries
- Static authentication
- Reactive threat response
But AI-driven environments invalidate these assumptions.
Today, identity is no longer a static checkpoint. It is a continuous variable that must be:
- Verified in real time
- Contextually validated
- Behaviorally monitored
Yet, 34% of Indian organizations report only partial visibility into identity access.
This is where the shift occurs.
Security evolves from a defensive layer into an experience orchestration engine. Every login, access request, and authentication flow becomes part of the user journey.
“Nearly 29% of Indian employees use more than 10 business applications daily, each representing a credential that must be governed and secured.” — Zoho Corp.
The implication is clear:
Without unified identity governance, complexity scales faster than control.
Strategy Is Misaligned: AI on Weak Foundations
The State of Workforce Password Security Report 2026 reveals a strategic misstep—organizations are prioritizing AI capabilities over foundational security maturity.
98% of organizations plan to deploy AI-driven security tools.
91% expect to increase security budgets.
Yet:
- Only 25% have strong password policies and MFA
- Just 9% prioritize access control
- Endpoint security sits at 16%
This imbalance exposes a flawed sequencing strategy.
“An AI ‘bandaid’ on these structural gaps will make the situation worse in the long-term.” — Chandramouli Dorai, Zoho Corp.
Strategically, this indicates a need to reverse the order of investment:
- Identity governance
- Access control
- Credential management
- Then AI augmentation
This is where the shift becomes unavoidable.
AI does not replace security fundamentals—it depends on them.
Competition Is Moving Faster on Identity Maturity
Globally, identity-first security is already a competitive differentiator.
Companies like Microsoft, Okta, and Cisco have:
- Mature Zero Trust frameworks
- Integrated identity ecosystems
- AI-enhanced threat intelligence
Meanwhile, Zoho is positioning itself with a unified, privacy-first stack spanning:
- Zoho Vault (credential management)
- Zoho Directory (IAM)
- Zoho OneAuth (passwordless MFA)
- Ulaa (secure enterprise browser)
This integrated approach reduces fragmentation—a critical factor in improving both security and experience consistency.
The deeper implication is this:
Competition is no longer about tools—it is about cohesive identity ecosystems.
Technology Stack: Identity as the Control Plane
At a system level, the report underscores a fundamental architectural principle:
Identity is the new control plane.
Each employee interacts with:
- Multiple applications
- Multiple credentials
- Multiple access layers
This creates exponential complexity.
AI can enhance:
- Real-time threat detection (76%)
- User behavior analytics (56%)
- Risk-based access control (55%)
But these capabilities rely on structured identity data.
Without:
- Centralized credential management
- Unified access policies
- Continuous authentication
AI becomes reactive instead of predictive.
This is where the shift becomes technical and experiential simultaneously.
Systems must transition from: Credential storage → Identity orchestration
CX Impact: Security as Experience Design
From a CX standpoint, the State of Workforce Password Security Report 2026 highlights a critical transformation—security is no longer invisible infrastructure. It is a visible part of the user journey.
Customer Layer
- Repeated authentication creates friction
- Inconsistent access reduces trust
- Security failures erode confidence
Business Layer
- Breaches increase operational costs
- Productivity declines due to access issues
- Support overhead rises
System Layer
- Identity fragmentation leads to blind spots
- Lack of visibility increases risk exposure
- Weak access controls enable insider threats
“Malicious insiders ranked as the single biggest threat at 23%.” — Zoho Corp.
This is where the shift becomes unavoidable.
Security must evolve into a frictionless yet robust experience layer.
Maturity Gap: Confidence vs Capability
The report exposes a disconnect between perception and reality.
- 87% believe their security stack is future-ready
- 85% are optimistic about adopting Zero Trust
Yet:
- One-third lack Zero Trust entirely
- Legacy infrastructure remains a major barrier (51%)
This creates a maturity illusion.
Organizations believe they are ready for the future—but are structurally anchored in the past.
The trigger for change is clear: AI adoption is accelerating faster than infrastructure modernization.
Decision Intelligence: What Leaders Must Recalibrate
The State of Workforce Password Security Report 2026 is ultimately a decision-making document.
Build vs Buy vs Partner
- Build: High cost, high complexity
- Buy: Faster deployment via integrated platforms
- Partner: Essential for ecosystem integration
Risk Assessment
- Insider threats are rising
- Identity sprawl is expanding
- AI misuse risk is increasing
Implementation Complexity
- Requires cross-functional alignment
- Demands process redesign
- Needs cultural adoption
The deeper implication is strategic:
Security is no longer an IT decision.
It is an enterprise-wide transformation initiative.
Industry Implications: Talent, Ecosystem, Competition
The findings reshape the broader ecosystem.
Talent
Demand will rise for:
- Identity security specialists
- AI-security hybrid roles
Ecosystem
- Growth of passwordless authentication
- Expansion of IAM platforms
- Increased reliance on integrated stacks
Competition
- Platform players will dominate
- Fragmented tools will decline
This becomes critical as organizations seek solutions that:
- Reduce complexity
- Improve visibility
- Enhance user experience
The Future: Identity Before Intelligence
The future of enterprise security will not be defined by how fast organizations adopt AI—but by how well they structure identity.
The State of Workforce Password Security Report 2026 makes this clear.
AI will:
- Accelerate detection
- Enhance automation
- Improve response
But only if:
- Identity systems are mature
- Access controls are enforced
- Visibility is complete
Final Takeaways
The State of Workforce Password Security Report 2026 is not a report about passwords.
It is a warning about priorities.
Organizations that:
- Invest in AI without identity governance
- Expand access without visibility
- Scale systems without control
Will face:
- Higher breach risks
- Poorer user experiences
- Increasing operational costs
The deeper implication is decisive:
Security is no longer a backend function.
It is a frontline experience layer.
And in that shift lies the future of enterprise CX.