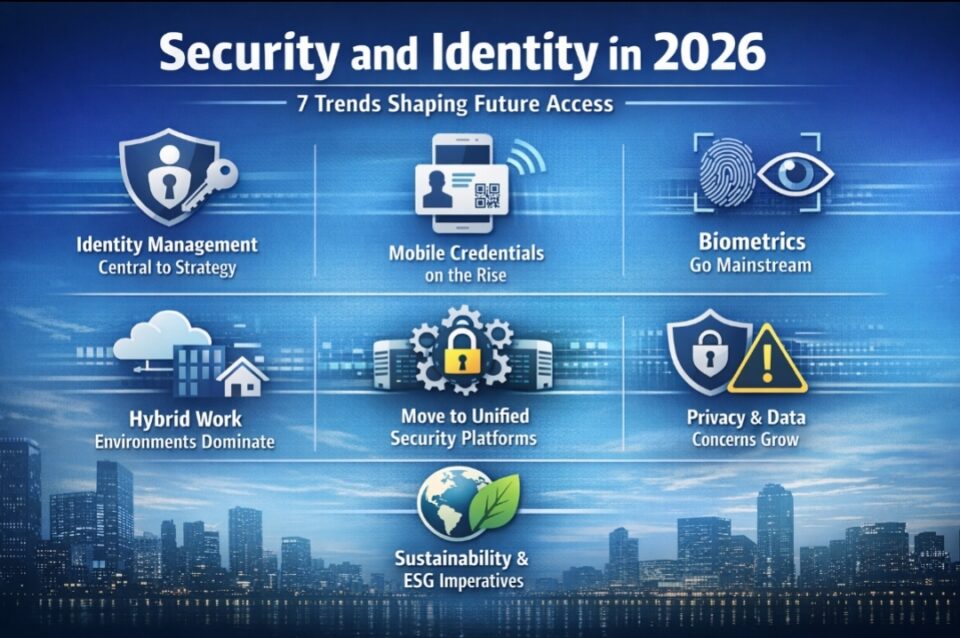
Security and identity convergence 2026 refers to the unification of physical and digital security systems into a single identity-driven platform. This shift matters because enterprises are moving from fragmented tools to integrated ecosystems, improving security, efficiency, and customer experience while addressing rising complexity and privacy concerns.
Security and Identity Convergence 2026 Is Redefining Enterprise Trust Architecture
Security is no longer defined by barriers—it is defined by identity. The latest report by HID Global, part of ASSA ABLOY, makes this shift explicit. The emergence of security and identity convergence 2026 signals a structural transformation in how enterprises design trust, access, and experience across physical and digital environments.
Based on a survey of over 1,500 security and IT leaders, the report shows that identity management is now the top priority, with 73% of respondents ranking it as a key strategic focus.
This is where the shift begins: security is no longer a function—it is an experience layer.
When Security Silos Collapse, Identity Becomes the System
For decades, enterprise security operated in silos. Physical security teams managed access cards and surveillance, while IT teams governed authentication systems. These parallel structures created inefficiencies, blind spots, and inconsistent user journeys.
Today, that model is breaking down.
“Security is entering a new phase where physical and digital identities are converging into a unified strategy.” — HID Global Report
This becomes critical when 84% of organizations operate in hybrid environments. Identity is now the only consistent layer across systems, users, and locations.
The deeper implication is structural: enterprises are no longer securing infrastructure—they are securing identity flows.
Security and Identity Convergence 2026 Is Driving a Platform Shift
At a structural level, security and identity convergence 2026 represents a transition from fragmented tools to integrated platforms.
The legacy model relied on:
- Physical access cards
- Password-based authentication
- Isolated monitoring systems
The emerging model integrates:
- Mobile credentials (adopted or planned by 74%)
- Biometrics (60% adoption trajectory)
- Real-time location systems and RFID
“Identity management has become the foundation for modern security strategies.” — HID Global Report
Strategically, this indicates a redefinition of enterprise control. Identity is no longer a subset of IT—it is the backbone of enterprise architecture.
Pull Quote:
“Identity management is now the #1 priority shaping security strategy.”
Integration Depth Is the New Competitive Advantage
The report highlights a critical friction point:
Over 50% of organizations cite managing multiple systems as their biggest challenge.
This is where the shift occurs.
“Integrating many security solutions into a single, manageable platform remains difficult.” — HID Global Report
The competitive landscape is no longer defined by feature innovation—but by integration depth.
Organizations that successfully unify identity, access, and context gain:
- Real-time visibility
- Faster decision-making
- Reduced operational friction
Pull Quote:
“The era of isolated security systems is giving way to unified identity ecosystems.”
Technology Fades, Experience Surfaces
At the technology layer, convergence integrates identity management, mobile credentials, biometrics, RTLS, and RFID into a unified architecture.
But the real transformation is experiential.
From a CX standpoint:
- Authentication becomes invisible
- Access becomes frictionless
- Security becomes embedded
“Mobile credentials adoption continues to rise as organizations seek both convenience and enhanced security.” — HID Global Report
This becomes critical when security directly shapes user experience—whether entering a facility, accessing systems, or tracking assets.
Pull Quote:
“The best security systems are the ones users don’t notice.”
Trust, Privacy, and the New CX Tension
While adoption is accelerating, trust is becoming the defining constraint.
The report reveals:
- 67% express concern about biometric privacy
- 29% cite privacy as a barrier to RTLS adoption
“Privacy and ethical concerns are rising as organizations adopt advanced identity technologies.” — HID Global Report
This introduces a new tension:
The more intelligent the system becomes, the more trust it must earn.
From a CX standpoint, this is resultive. Security systems must balance:
- Protection
- Transparency
- User choice
Pull Quote:
“Security without trust is friction. Trust without security is risk.”
Maturity Is Rising—But Execution Remains Uneven
8 in 10 organizations are evaluating or deploying converged solutions. Yet, maturity gaps persist.
The primary barriers:
- Cost concerns (44%)
- Lack of expertise (37%)
- Perceived complexity (32%)
“Organizations are increasingly investing in integration, but execution challenges remain significant.” — HID Global Report
This becomes critical when strategy outpaces capability. Enterprises understand the “what” and “why”—but struggle with the “how.”
Decision Intelligence: Why Partner Ecosystems Will Win
The report implicitly points toward a clear conclusion: convergence cannot be achieved in isolation.
Enterprises face three paths:
- Build → high control, high complexity
- Buy → fast but fragmented
- Partner → integrated and scalable
“Successful organizations will partner with providers who can bridge expertise gaps and support long-term integration.” — HID Global Report
The deeper implication is ecosystem-driven success. Integration capability—not ownership—will define winners.
Industry-Wide Implications Extend Beyond Security
The impact of security and identity convergence 2026 extends across the enterprise:
- Talent: Demand for hybrid expertise (IT + physical security)
- Competition: Platform providers will dominate
- Ecosystem: Integrators become critical enablers
Additionally, industries like healthcare, manufacturing, finance, and government are accelerating adoption—expanding the role of identity beyond security into operations and compliance.
This becomes critical when integration—not innovation—becomes the primary bottleneck.

The Future: Identity as the Enterprise Backbone
The direction is unmistakable.
“Integration is no longer a project—it is the operating model for modern security.” — HID Global Report
In this future:
- Access is dynamic and context-aware
- Security is continuous
- Experience is seamless
The deeper implication is strategic: enterprises are not just upgrading systems—they are redefining how trust is built and delivered.
Security and identity convergence 2026 is not a trend to observe. It is a transformation to execute.
Final Takeaways
- Identity is replacing infrastructure as the core security layer
- Integration capability is the new competitive advantage
- Security is evolving into a CX function
- Privacy and trust will define adoption success
- Partner ecosystems will drive execution at scale
Enterprises that understand this shift—and operationalize it—will not just improve security. They will redefine experience, efficiency, and trust in the digital-first world.
Security and identity convergence 2026 marks a shift from fragmented systems to unified identity platforms, redefining enterprise trust and CX.